I recently encountered an intriguing campaign that uses fake websites to distribute malware. While this technique (TTP) is not new, it appears to be increasing in frequency. From my own observations, I’ve noticed this happening more often in 2023 compared to previous years. Though it’s hard to quantify without in-depth research, it’s something that other […]
Category Archives: Uncategorized
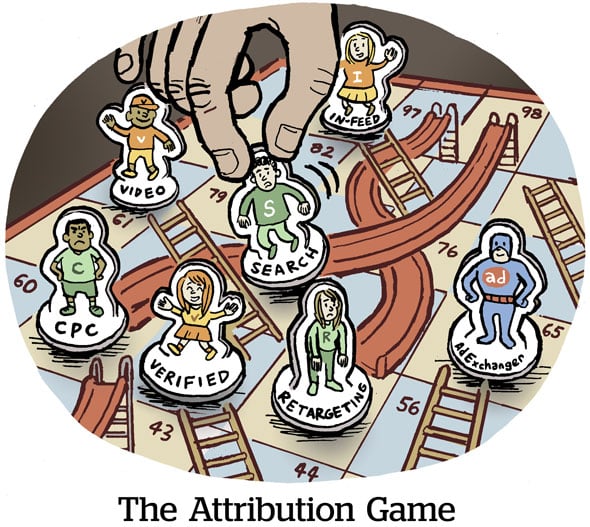
A “dead drop” is a well-known espionage tactic of passing items or information between two parties using secret locations. The two parties never meet and any sign of communication is concealed. This tactic is commonly used by intelligence officers to interact with their assets in the field to avoid any suspicious meetings or either caught […]
Background A point of sale (POS) system refers to the critical piece of software used by customers to execute a payment for goods or a service. This also includes the physical devices in stores, where POS terminals and systems are used to process card payments. These are often the primary targets of financially motivated organised […]
In 1937, one of the world’s most authoritative art historians, Abraham Bredius, was approached by a lawyer on behalf of a Dutch family estate to inspect a painting of a Christ and the Disciples at Emmaus (pictured above). Bredius dedicated many years of his life studying the artwork of Johannes Vermeer. After inspecting the painting, […]
A new web skimmer called “Meyhod” has recently been disclosed by RiskIQ. Named after a typo in its code, this malware first surfaced in October, targeting several e-commerce sites, including Bosley, a hair treatment company, and the Chicago Architecture Center (CAC). While investigating the attacker’s domain (jquerycloud[.]com) a bit further and other potential victims from […]